Hackers drain $1.5 million worth of bitcoin ATMs by exploiting 0-day flaw – Ars Technica
General bytes
Hackers siphoned millions of dollars in digital coins from cryptocurrency ATMs by exploiting a zero-day vulnerability, leaving customers on the hook for losses that cannot be reversed, the kiosk maker has revealed.
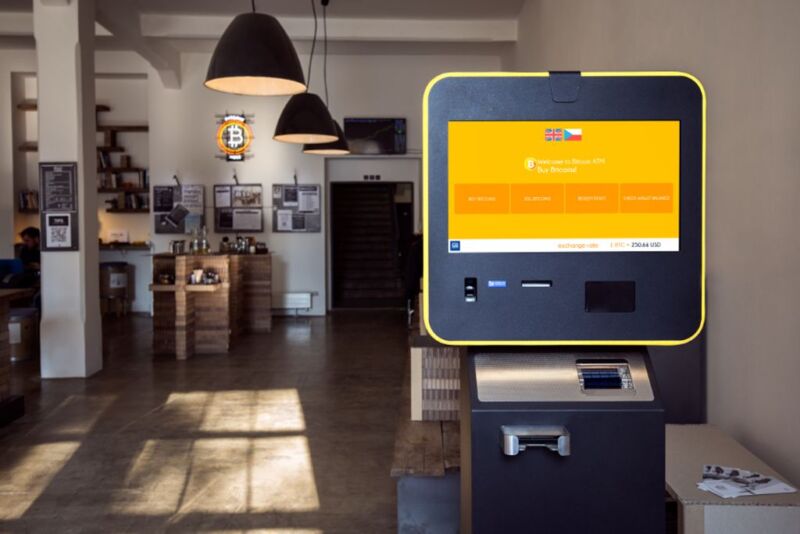
The robbery targeted ATMs sold by General Bytes, a company with multiple locations around the world. These BATMs, short for bitcoin ATMs, can be set up in convenience stores and other businesses to allow people to exchange bitcoin for other currencies and vice versa. Customers connect the BATMs to a crypto application server (CAS) that they can manage or, until now, that General Bytes could manage for them. For reasons that are not entirely clear, the BATMs offer an option that allows customers to upload videos from their terminal to the CAS using a mechanism known as the master server interface.
Going, going, gone
Over the weekend, General Bytes revealed that more than $1.5 million worth of bitcoin had been drained from CASs run by the company and by customers. To complete the heist, an unknown threat actor exploited a previously unknown vulnerability that allowed it to use this interface to upload and run a malicious Java application. The actor then drained various hot wallets of around 56 BTC, worth approximately $1.5 million. General Bytes patched the vulnerability 15 hours after learning about it, but due to the way cryptocurrencies work, the losses were irreversible.
General Bytes officials wrote:
The night 17.-18. March was the most challenging time for us and some of our customers. The entire team has been working around the clock to collect all data regarding the security breach and is continuously working to resolve all cases to help customers get back online and continue to operate their ATMs as soon as possible. We apologize for what happened and will review all of our security procedures and are currently doing everything we can to keep our affected customers afloat.
The post said the flow of the attack was:
1. The attacker identified a security vulnerability in the main service interface that BATM uses to upload videos to CAS.
2. The attacker scanned the IP address range managed by the DigitalOcean Ocean cloud host to identify running CAS services on ports 7741, including the General Bytes Cloud service and other BATM operators running their servers on Digital Ocean.
3. By exploiting the vulnerability, the attacker directly uploaded the Java application to the application server used by the admin interface. By default, the application server was configured to launch applications in the distribution folder.
When the malicious application was run on a server, the threat actor was able to (1) access the database, (2) read and decrypt encrypted API keys needed to access funds in hot wallets and exchanges, (3 ) transfer funds from hot wallets to a wallet controlled by the threat actor, (4) download username and password hashes and disable 2FA, and (5) access terminal event logs and scan for instances where customers scanned private keys at the ATM. The sensitive data in step 5 was logged by older versions of ATM software.
BATM customers on their own now
Going forward, said this weekend’s post, General Bytes will no longer manage CASs on behalf of customers. This means that terminal owners must manage the servers themselves. The company is also in the process of collecting customer data to validate any losses related to the hack, conduct an internal investigation, and cooperate with authorities in an effort to identify the threat actor.
General Bytes said the company has received “multiple security audits since 2021” and that none of them discovered the exploited vulnerability. The company is now in the process of seeking further assistance to secure its BATMs.
The incident underscores the risks of storing cryptocurrencies in internet-accessible wallets, often referred to as hot wallets. Over the years, hot wallets have been illegally drained for countless amounts of digital coin by attackers exploiting various vulnerabilities in cryptocurrency infrastructures or by tricking wallet holders into providing the encryption keys required to make withdrawals.
Security practitioners have long advised people to store funds in cold wallets, meaning they are not directly accessible to the Internet. Unfortunately, BATMs and other types of cryptocurrency ATMs generally cannot follow this best practice because the terminals need to be connected to hot wallets so that they can perform transactions in real time. That means BATMs are likely to remain a prime target for hackers.


